June 1st, 2026 by admin
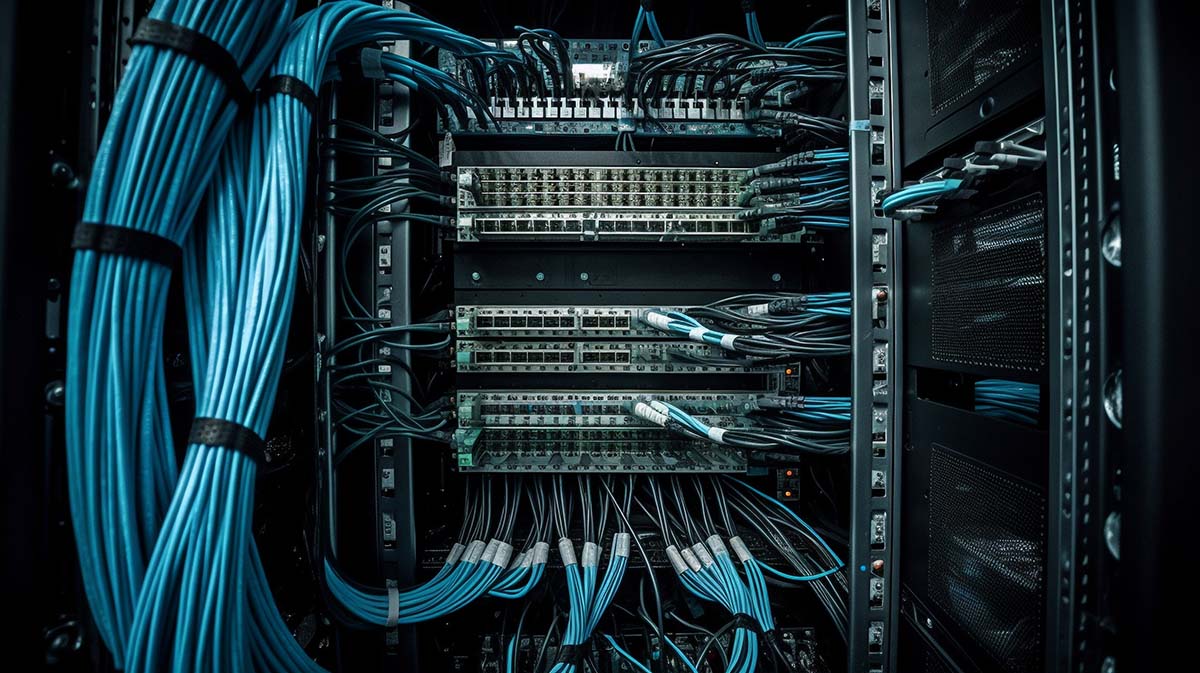
Understanding the Modern Telecom Carrier Landscape
The telecommunications industry has undergone a dramatic transformation over the past decade. What was once a straightforward decision between a handful of local providers has evolved...
Read Full Story »
Tags: productivity, service provider, telecommunications
Posted in: Services
May 15th, 2026 by admin
Why Cloud Technology Matters for Midsize Business Success
Midsize businesses occupy a unique position in the technology landscape. Unlike enterprise organizations with extensive IT departments and unlimited budgets, or small businesses...
Read Full Story »
Tags: benefits, business, cloud
Posted in: Solutions